Why do we need blockchain 3? ELI5
Let us explore one of the core features of Blocklchain in detail
Hey Folks,
So far we have covered what is blockchain and how it works, then we covered its features and discussed different types of blockchains such as Public, Private and Federated.
Recap
To refresh your memory kindly check out below links :
The core verticals of blockchain are :
Cryptography
Consensus
Distributed Ledger
Intro to Cryptography
This week, we will deep dive into Cryptogrpahy, and how it is applied in Blockchain’s architecture, Cryptography is the art of writing and solving puzzles, will digress a bit
Alan Turing aka Father of AI/Comp Sci, basically all the cool tech stuff we aspire to work for today, developed a machine that solved puzzles and replaced human computers, more on this here
In modern days cryptography is aimed at making messages unreadable to unauthorised readers. It is also meant for digital signing, verification to protect data privacy, and confidential communications like emails and credit card transactions.
Let us first look at the basic terminology :
Plain test(M) : The message to encode
Encryption(E) : Encoding if the message
Cipher text(C) : Encrypted message
Decryption(D) : Decoding of the cipher text
There are 2 functions : One encodes(Encryption) and other decodes(Decryption)
E(M) = C, D(C) = M
D(E(M)) = M
The game lies in secrecy of the algorithm, but with the advent of internet and social media, and info traveling at lightspeed, that is hard. But if you can’t hide it then make it super confusing to understand right ?
For extra curious folks who want to see this cryptography in action try here, Decrypted Hello World is 2aae6c35c94fcfb415dbe95f408b9ce91ee846ed, when you apply basic SHA1 hashing, play around with that site, do some ciphering and trouble your friends
Key Based Cryptography
So, Key based cryptography was born, let us look at it in more detail, now this key for both encryption and decryption can be same or different, basis on this symmetry we have 2 types of Cryptography :
Symmetric Key Cryptography
Asymmetric Key Cryptography
then this key(K2, usually the public one) is shared with Receiver, to read the cipher
here is the catch, the key must not be shared along with the message, else anyone in the process can tap in and decipher the message, so key ,must be shared separately from the message
Symmetric key cryptography is fast but un-secure(as sharing one key jeopardises its secrecy), Asymmetric is safe but energy intensive.
Let us look at properties of these secret keys:
Confidentiality : Only select people can read the message
Authentication : The person with key is the real/supposed receiver/sender
Integrity : Data was not tampered with
Non-repudiation : That sender can’t deny sending it, as the key confirms he did send it or the key was stolen
Algorithms for Key based Cryptography
Started with DES and now we use AES as standards of cryptography
Most commonly used algos in blockchain are :
DES
AES
DES : Data encryption standard (DES) has been found vulnerable to very powerful attacks and therefore, the popularity of DES has been found slightly on the decline. DES is a block cipher and encrypts data in blocks of size of 64 bits each, which means 64 bits of plain text go as the input to DES, which produces 64 bits of ciphertext. The same algorithm and key are used for encryption and decryption, with minor differences. The key length is 56 bits.DES is based on the two fundamental attributes of cryptography: substitution (also called confusion) and transposition (also called diffusion)
AES : AES, Advanced Encryption Standard, is a block cipher. The key size can be 128/192/256 bits. Encrypts data in blocks of 128 bits each. That means it takes 128 bits as input and outputs 128 bits of encrypted cipher text as output. AES relies on substitution-permutation network principle which means it is performed using a series of linked operations which involves replacing and shuffling of the input data.
Hash function :
Takes an arbitrary length string as input and produces a fixed size output(eg. 256 bits), it is easy to compute but almost impossible to reverse.
Security properties :
collision resistance
hides the original string
puzzle friendly
Collision resistance :
Ex. Find x and y(where x<>y), such that H(x)= H(y)
Basically no two objects can give same hash value(this is impossible)
why we need this : if the file is corrupted due to transfer, the hash will never match if there is any form of tampering in the file so it is a kind of way to verify the authenticity of the data/file, a hacker can suitably modify the file such as to keep the hash value same, corrupting the base data
Technically a hash function can never be collision free, but collision resistant
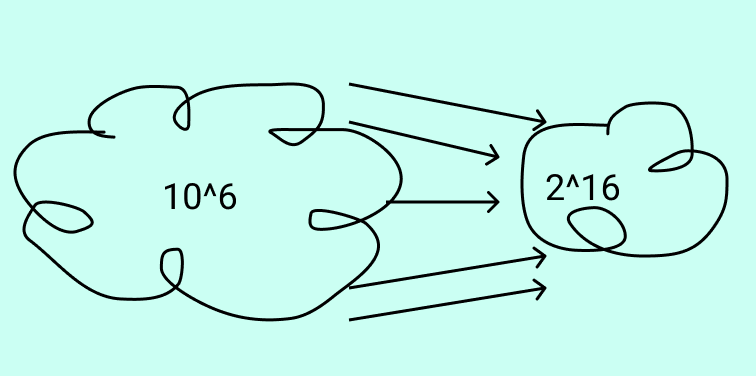
if one were to convert all numbers till 6 digits into 16 bit hashes, so possible input can be 10^6, but possible output will be 2^16, so some values will have same hashes, but they should be hard to findHash Pointer
So a regular pointer stores the address of the data, attacehd the hash of the data to this pointer and you got a hash pointer. These hashpointers are the building blocks for Merkle Trees and Block Chain
Data structures in Blockchain
Blockchain is a combination of Two data structures, Linked lists and Merkle trees
Linked list- This is the structure of the blockchain itself, which is a linked list of hash pointers. A regular linked list consists of nodes. Each node has 2 parts- data and pointer. The pointer points to the next node. In the blockchain, simply replace the regular pointer with a hash pointer.
Merkle tree- A Merkle tree is a binary tree formed by hash pointers, and named after its creator, Ralph Merkle.
ex. Estonia has docs in hash trees, forming a calendar blockchian(merkle + linked hash), and voting is blockchain……https://irishtechnews.ie/blockchain-e-voting-is-real-where-how-when/